Study Guide Notes For This Lesson
These are the words that are displayed and spoken during the lesson. Get these notes for the whole course in the Certification Study Guide, available in print or eBook. Many people tell us a printed companion book enhances their learning!
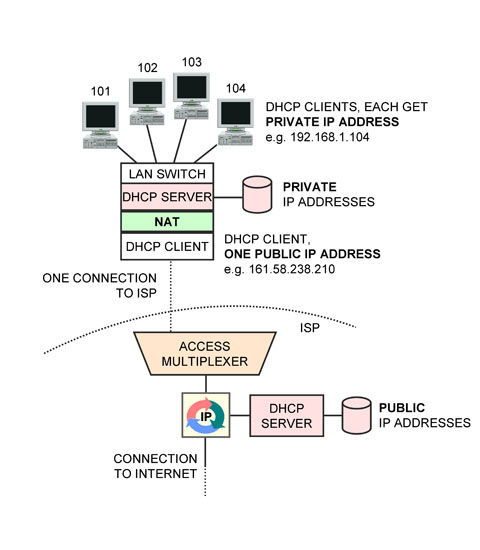
In the previous lesson, we covered private IP addresses, and why these were preferable to use on an in-building network.
We also noted that if any of the users on the private network want to receive packets from the Internet, a public IP address is required.
The question we explore in this lesson is how to enable Internet communications for all users in-building without having to rent a public IP address for every user?
A solution is to use a Network Address Translator (NAT).
When a computer on the private side initiates communications with a server, it populates the source IP address field in the packet header with its private address and the destination IP address field with the public IP address of the server.
The packet is then transmitted in a MAC frame to the computer's "default gateway", which is the Customer Edge router. This device is performing the NAT function. The NAT changes the source IP address from the private IP address of the sender to the public IP address of the NAT, i.e. the CE router, then transmits the packet in a frame on the public network (the Internet).
The Internet server of course uses the source address in the packet it receives as the destination address to answer back to the client. Therefore, it will send the response back addressed to the NAT.
When the NAT receives the packet, it changes the destination IP address on the packet received from the Internet to the private IP address of the appropriate computer, then transmits the packet in a MAC frame to the computer.
How does the NAT know what computer on the private network a packet received from the Internet is intended for?
It turns out that the NAT uses the Layer 4 header to keep track of things.
The Layer 4 header (TCP or UDP) begins with two octets that are called the "source port" then two octets for the "destination port". These fields are used to indicate which application on a computer the message is being sent from and to.
The NAT selects an arbitrary "fake" port number to identify a computer on the private network, and records this port number against the private address in a table.
When a packet is transmitted to the Internet, the NAT records the actual source port number then changes the source port value to the "fake" port number.
When the reply from the server is received from the Internet, it has the "fake" port number in the destination port field of the Layer 4 header. The NAT uses this to look up the correct private IP address and correct port number and enter those values in the destination address and destination port number fields, thus relaying the incoming packet to the correct computer on the private network.
NAT provides a number of advantages
1. A NAT allows multiple computers in-building to share a single Internet address and Internet connection.
2. A NAT provide a truly "always-on" connection to the Internet. Services like DSL and Cable modem described as "always on" are always connected at the Physical Layer. They do not provide "always on" at the Network Layer, since DHCP must be run every time the attached device restarts to get a public IP address.
When a NAT is inserted, it runs DHCP to get the public IP address; so if the NAT is not powered off, the site will always have a public IP address assigned, and thus a connection to the Internet always ready for immediate use.
3. A NAT shields machines from attacks from the Internet. Since a private IP address is not reachable from the Internet, there is no way for a machine on the Internet to initiate communications to a machine on the private network. The only device exposed to the Internet is the NAT. Normally, the NAT is not running on a computer running Windows, so attackers have a greatly diminished chance of finding an vulnerability to exploit compared to connecting a computer running Windows naked onto the Internet.
Devices that perform this function are available in industrial-strength versions from companies like Cisco.
Hardware devices to do this are also available for about $20 from companies like Linksys for use on a DSL or cable modem connection. They often include both an Ethernet switch and an 802.11 wireless LAN access point for the private network side.
Most ISPs now provide the CE router with NAT function integrated in a device that includes the DSL or Cable modem they supply.














 Network Address Translation (NAT)
Network Address Translation (NAT)